
Verizon Caught Blocking VoIP Traffic
I was just on a phone call with a new customer who is setting up multiple retail locations. The reason for the call was their backup network wasn’t working. Whenever they tested the Verizon 4G LTE Wireless connected to Cradlepoint modem backup network, the phones would not be able to make or receive phone calls.
Their IT staff was on the line and they were running Wireshark and grabbed a PCAP that seems to show that OnSIP at 199.7.175.101 was responding to their request with a “500 Server Error”.
![]()
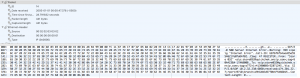
The actual text was:
SIP/2.0 500 Server Internal Error
Warning: 399 sipalg “Internal Error”
Call-ID: b876f6fb4aad25a55546217e07dd4f82
CSeq: 47 REGISTER
From: “Store 032” <sip:store032@quickchek.onsip.com>;tag=50A423BA-17AAB00B
To: <sip:store032@quickchek.onsip.com>;tag=s772+1+41390005+52871245
Via: SIP/2.0/UDP 10.2.32.238:6050;received=174.201.22.7;rport=9710;branch=z9hG4bKd5770b4F5466015
Content-Length: 0
The only problem was that the packet did not come from OnSIP. The smoking gun in the second line which references the “sipalg”. Even though the PCAP shows the packet as coming from OnSIP, it really comes from the Verizon SIP ALG running on their network or running on the Cradlepoint router.
Not only are they blocking the traffic, but they’re making it look like the provider is actually the one refusing it. At least if you’re going to block traffic, let everyone know who is doing it.
HTTP traffic from the same device to the same network goes through without an issue, only the SIP traffic is refused.
Is this the future of Net Neutrality? We saw this behavior a few years ago and it appears to still be an issue.


2 Comments
Colton Conor
Why not just use TLS to get around this?
Mike
Not all phones support TLS or TCP for that matter. And it requires the provider to support that as well. Most do not. OnSIP does, but we’re an outlier.